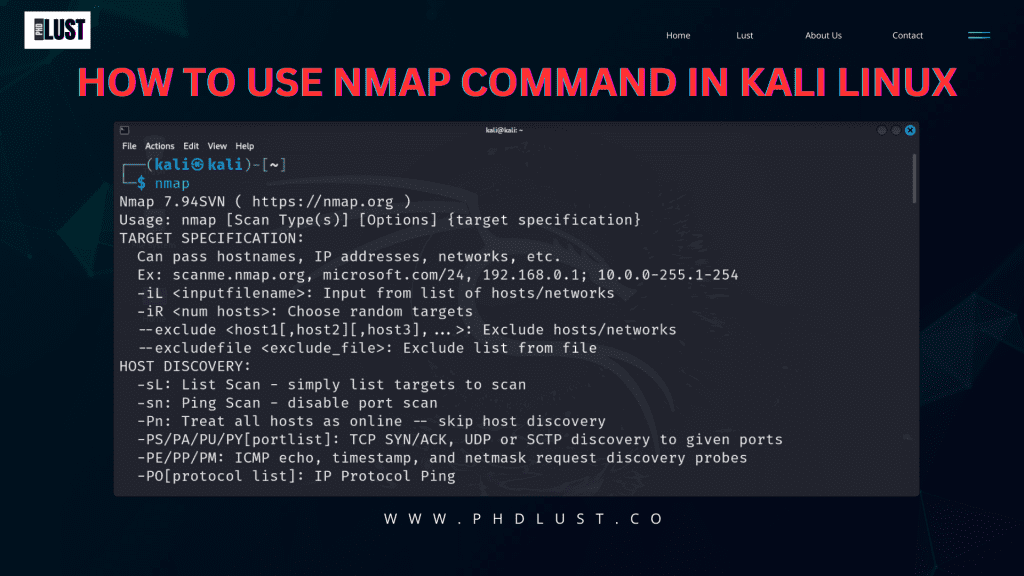
How to Use Nmap Command in Kali Linux
For Quick information : Web story
NMAP– Network Mapper, is a powerful open-source tool used for network discovery and security auditing. It is widely used by network administrators, security professionals, and ethical hackers to explore networks, identify vulnerabilities, and secure systems.
In this article, we will see that how to use the Nmap-command in Kali Linux
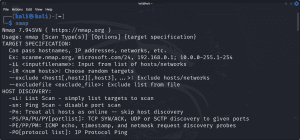
1. Introduction to Nmap Command
Nmap is a command-line tool that allows users to discover hosts and services on a computer network by sending packets and analysing the responses. It can be used to perform various types of scans, including port scanning, version detection, and OS fingerprinting. first step to enter into cyber security field , basically it’s part of our recon
2. Installing Nmap on Kali Linux
I know it’s stupid question because we all know that nmap by default provided in kali Linux. but Before using Nmap, you need to ensure it is installed on your Kali Linux system. You can install Nmap as well update it your kali Linux by using the following command in the terminal:
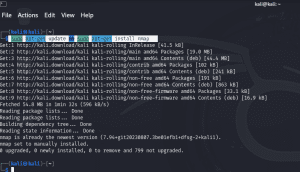
sudo apt-get update
sudo apt-get install nmap
3. Basic Usage of Nmap
Open a terminal window in Kali Linux and you given cmd and try it with me .
if you are beginner and don’t know where to start so this is right place for you.
To get your target ip address you can also go with direct target domain name : get target ip address through
ping domain.com
and you get your target ip address and to stop that cmd(ping process) ctrl + c
nmap [scan type] [options] [target]
For example, to perform a TCP connect scan on a target host, you can use the following command:
nmap -sT target_ip
nmap -n target_ip
-n: This option instructs Nmap to skip DNS resolution during the scan. By using this option, Nmap will not attempt to resolve hostnames for the IP addresses it scans.
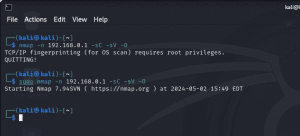
Root Privileges :
sometime nmap need root (sudo) privileges . i added screenshot below check out if don’t what different . only add sudo at start and your default kali password : kali (you can’t see it but just type it and hit enter ) . don’t confused by cmd just scroll down to know my entered screenshot cmd meaning .
4. Scanning Techniques
Nmap supports various scanning techniques, each with its advantages and disadvantages. Some common scanning techniques include:
TCP Connect Scan
nmap -sT target_ip
This scan establishes a full TCP connection with the target port, making it easily detectable but more reliable.
SYN Stealth Scan
nmap -sS target_ip
Also known as a half-open scan, this scan sends SYN packets to the target ports without completing the TCP handshake, making it less detectable but faster.
UDP Scan
nmap -sU target_ip
This scan is used to discover UDP services running on the target host.
Comprehensive Scan
nmap -sC -sV target_ip
- -sC : equivalent to –script=default
- -sV : Probe open ports to determine service/version info
This command performs a comprehensive scan on the target IP address. It combines multiple scanning techniques, including default scripts (-sC) and version detection (-sV), for a thorough analysis.
Most use and helpful cmd , I personally use this cmd most.
5. Output Formats
Nmap provides several output formats to display scan results, including text, XML, and grepable formats. You can specify the desired output format using the -o option followed by the format type. Examples also given below :
For example, to perform a SYN scan and output the results in XML format, you can use:
nmap -sS -oX scan_results.xml ip address
- -oN <file>: normal format.
- -oX <file>: XML format.
- -oS <file>: s|<rIpt kIddi3 format.
-oG<file>: Grepable format. - -v: Increase verbosity level (use -vv or more for greater effect)
-d: Increase debugging level (use -dd or more for greater effect)
6. Scripting with Nmap
Nmap includes a scripting engine that allows users to write and execute scripts to automate tasks and perform advanced scanning techniques.
nmap --script vuln target_ip
Replace <target_ip> with the IP address of the system you want to scan for vulnerabilities.
Maybe if you need to see some live or recoded tutorial for better understanding.
Hindi audio : youtube.com/watch?v=U6-TtLMD_2I
7. Nmap for Network Discovery
Nmap can be used for network discovery to identify active hosts, open ports, and services running on a network.
nmap -sn 192.168.1.0/24
In this command:
-sn: specifies a ping scan, which means Nmap will only ping the target hosts to see if they are up.192.168.1.0/24: is the IP range you want to scan. Replace it with the appropriate network range for your environment.
8. Nmap for Security Auditing
Security professionals use Nmap for security auditing to identify vulnerabilities and weaknesses in network systems and devices.
nmap -p 1-65535 -sV -sS -T4 target_ip
In this command:
-p 1-65535specifies that Nmap should scan all 65,535 TCP ports to uncover potential open ports and services.-sVenables version detection-sSexecutes a SYN scan-T4sets the timing template to aggressive, speeding up the scan while maintaining reliability.
Timing options :
Timing options allow you to control the speed and aggressiveness of the scan. Here’s a brief overview of each timing option:
-T1: This is the slowest timing template in Nmap. It performs the scan very slowly and minimizes the impact on the network and target systems. To avoid detection.-T2: The-T2timing template is slower than the default timing but faster than-T1.-T3: This is the default timing template in Nmap.-T4: The-T4timing template is more aggressive than the default timing. It speeds up the scan by sending packets more rapidly and decreasing the time between probes.-T5: This is the fastest timing template in Nmap. It performs the scan very aggressively and quickly, which may increase the likelihood of detection by intrusion detection systems (IDS) or firewalls.
9. Tips and Tricks
- Always obtain permission before scanning a network.
- Use Nmap’s timing options to control the speed and stealthiness of your scans.
- Familiarize yourself with Nmap’s command-line options and scanning techniques.
- Keep Nmap updated to ensure you have the latest features and security patches.
10. Conclusion
In conclusion, Nmap is a versatile and powerful tool for network exploration and security auditing. By understanding how to use Nmap effectively, you can enhance your network troubleshooting and security assessment capabilities. I hope this article solve your searching query.
FAQs
No, Nmap should only be used for ethical hacking and security testing with proper authorization.
Nmap has a learning curve, but with practice and experimentation, you can master its features.
No, Nmap can only detect vulnerabilities exposed through network services.
Yes, Nmap is available for Windows, Linux, and macOS platforms.
It is recommended to update Nmap regularly to ensure you have the latest features and security fixes.
Author : [ ultroidxTeam ] Thank you follow or bookmark this page for more cyber security related article… once again thank you ! feel free to leave your query in comment box.