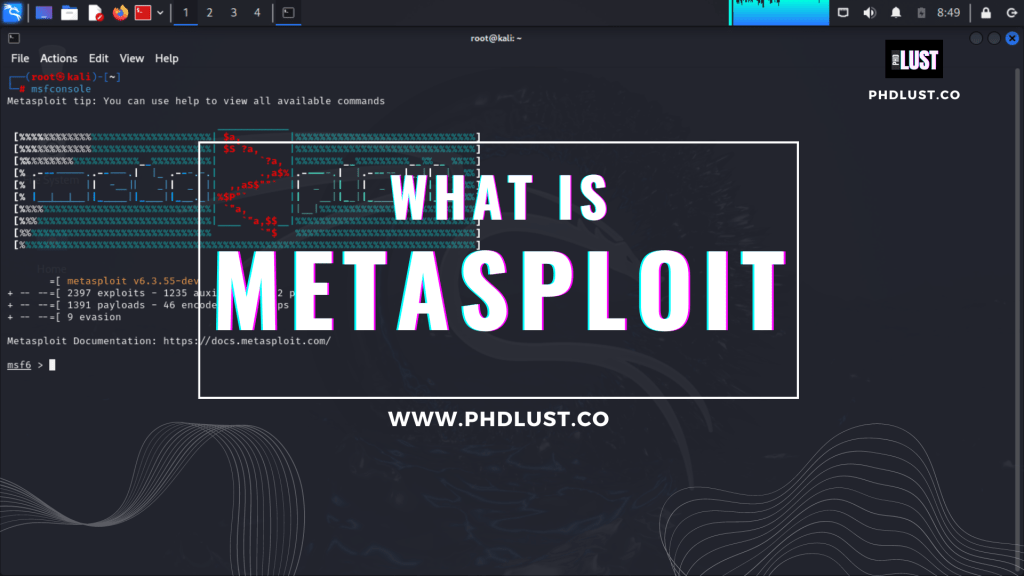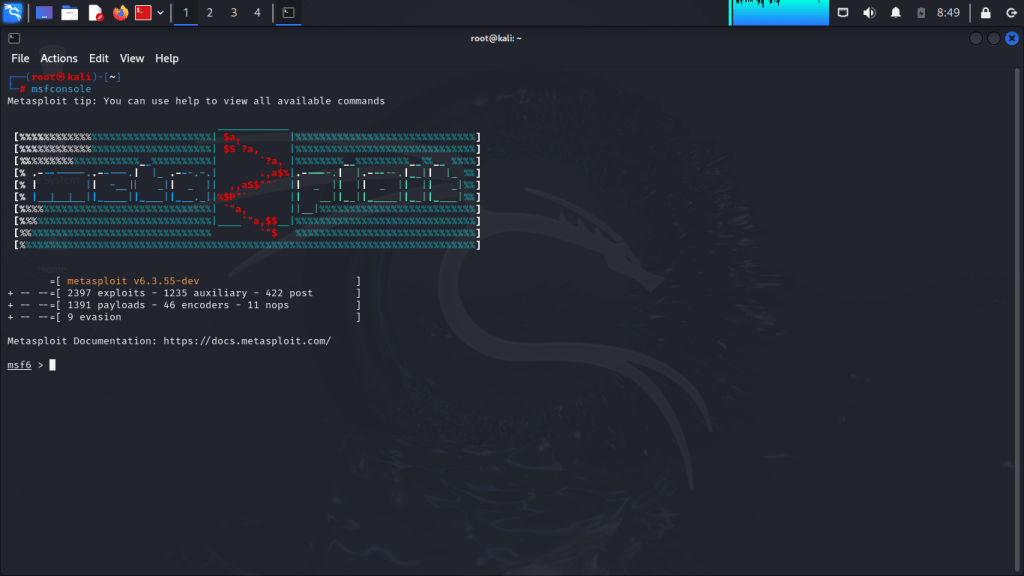
Welcome to our guide on understanding the basics of the Metasploit Framework. In this article, we’ll know the fundamental concepts of Metasploit and its significance in the realm of cybersecurity and to make this information more understandable I add some screenshots and check out list table .
What is Metasploit Framework?
The Metasploit Framework is an open-source cybersecurity project and The world’s most used penetration testing framework that provides information about security vulnerabilities and aids in penetration testing and IDS signature development. It offers a comprehensive suite of tools for ethical hacking and security research and using Metasploit our work being super fast and easy by just using some msfconsole (Metasploit). If you’re using Kali Linux, Metasploit is already pre-installed. See the Kali documentation for how to get started using Metasploit in Kali Linux but first complete your reading with maximum of your focus.
If some ask you ! what is Metasploit : Now You can say it that it’s framework and it’s inbuild available on kali linux
History and Evolution
In 2003, H.D. Moore created Metasploit, originally as a basic exploit framework. Over time, it grew into a comprehensive platform thanks to contributions from a thriving community. By 2007, it was fully transitioned to Ruby, and in 2009, Rapid7 acquired its license. Parts of other tools are now integrated into Metasploit, which comes pre-installed in the Kali Linux operating system. Rapid7 has further expanded its offerings with two proprietary tools, Metasploit Pro and Metasploit Express.
Components of Metasploit Framework
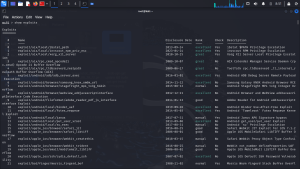
Exploits
Exploits are pieces of code that take advantage of vulnerabilities in software or systems.
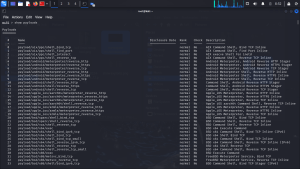
Payloads
Payloads are scripts or code snippets that execute a desired action on a compromised system, such as installing a backdoor or capturing keystrokes.
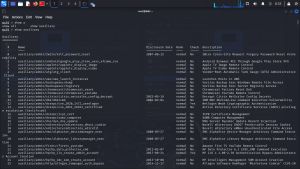
Auxiliary Modules
Auxiliary modules provide additional functionalities like scanning, fingerprinting, and brute-force attacks.
How Metasploit Works
Vulnerability Scanning
Metasploit facilitates vulnerability scanning to identify weaknesses in target systems.
Exploitation
Once vulnerabilities are identified, Metasploit enables the exploitation of these vulnerabilities to gain unauthorized access.
Post-exploitation
Post-exploitation involves maintaining control over the compromised system, allowing security professionals to gather information or execute further attacks.
Benefits of Using Metasploit
The Metasploit Framework empowers cybersecurity professionals with efficient testing capabilities, aiding in the identification and remediation of vulnerabilities.
Limitations and Risks
Despite its efficacy, Metasploit isn’t devoid of limitations and risks. Misuse of the framework can lead to legal repercussions, emphasizing the importance of ethical use.
Applications and Industries
Metasploit finds applications across various industries, from IT to finance, healthcare to government sectors. Its widespread adoption underscores its relevance in fortifying digital infrastructures against evolving threats.
Metasploit in Cybersecurity Training
Aspiring cybersecurity professionals often leverage Metasploit as a learning tool, honing their skills in ethical hacking and penetration testing.
Example: Exploiting a Vulnerability
Let’s consider an example scenario where Metasploit is used to exploit a known vulnerability in a web application. Suppose there’s a web server running an outdated version of Apache Struts, which is known to have a critical vulnerability. An attacker can use Metasploit to exploit this vulnerability and gain unauthorized access to the server.
Conclusion
In conclusion, the Metasploit Framework remains a pivotal asset in cybersecurity arsenals, offering a potent combination of functionality, flexibility, and community support. Embracing ethical principles and staying abreast of developments ensures its efficacy in safeguarding digital assets.
FAqs :
Yes, using Metasploit is legal, but it’s important to use it for ethical purposes like hacking and penetration testing. However, make sure to follow ethical guidelines and get proper permission before testing.
Absolutely! Metasploit is designed with an easy-to-use interface and comes with extensive documentation, making it accessible even for beginners in cybersecurity. However, having a good understanding of cybersecurity basics is recommended.
Using Metasploit incorrectly can have serious consequences, including legal trouble for unauthorized access. Additionally, using automated exploits without caution can lead to unintended outcomes. It’s important to use Metasploit responsibly and ethically.
While Metasploit is known for its offensive capabilities in cybersecurity, it also offers tools for defensive purposes like scanning for vulnerabilities and managing patches.
Metasploit is regularly updated by its community of contributors to stay ahead of evolving cybersecurity threats. These updates include new exploits, payloads, and features to keep the framework effective and up-to-date. cmd : 1. apt-get update && apt-get upgrade && apt-get dist-upgrade 2. Also msfupdate